1. Introductions and requirements
2. Get Roksnet member code
3. Software information
4. Install security server
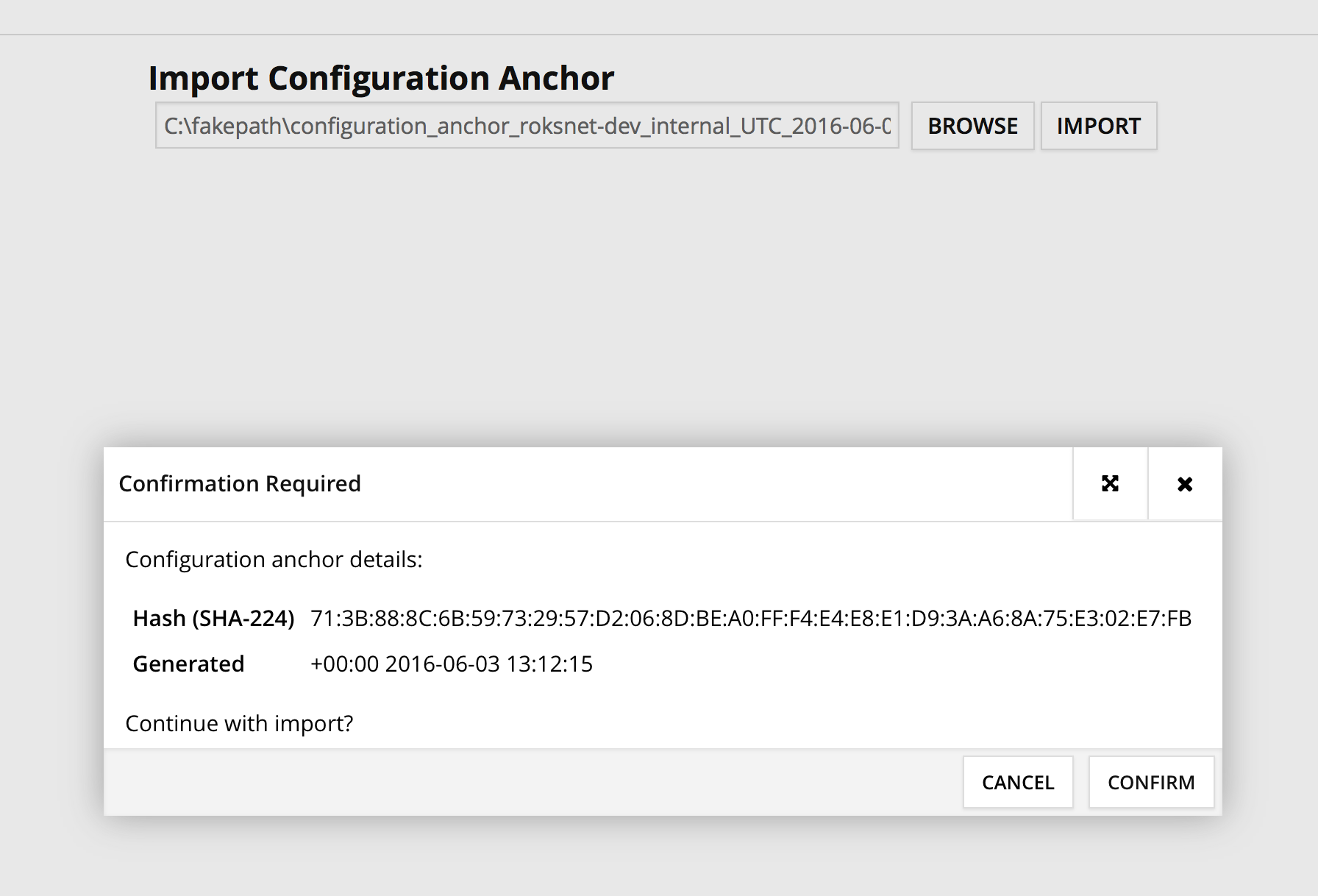
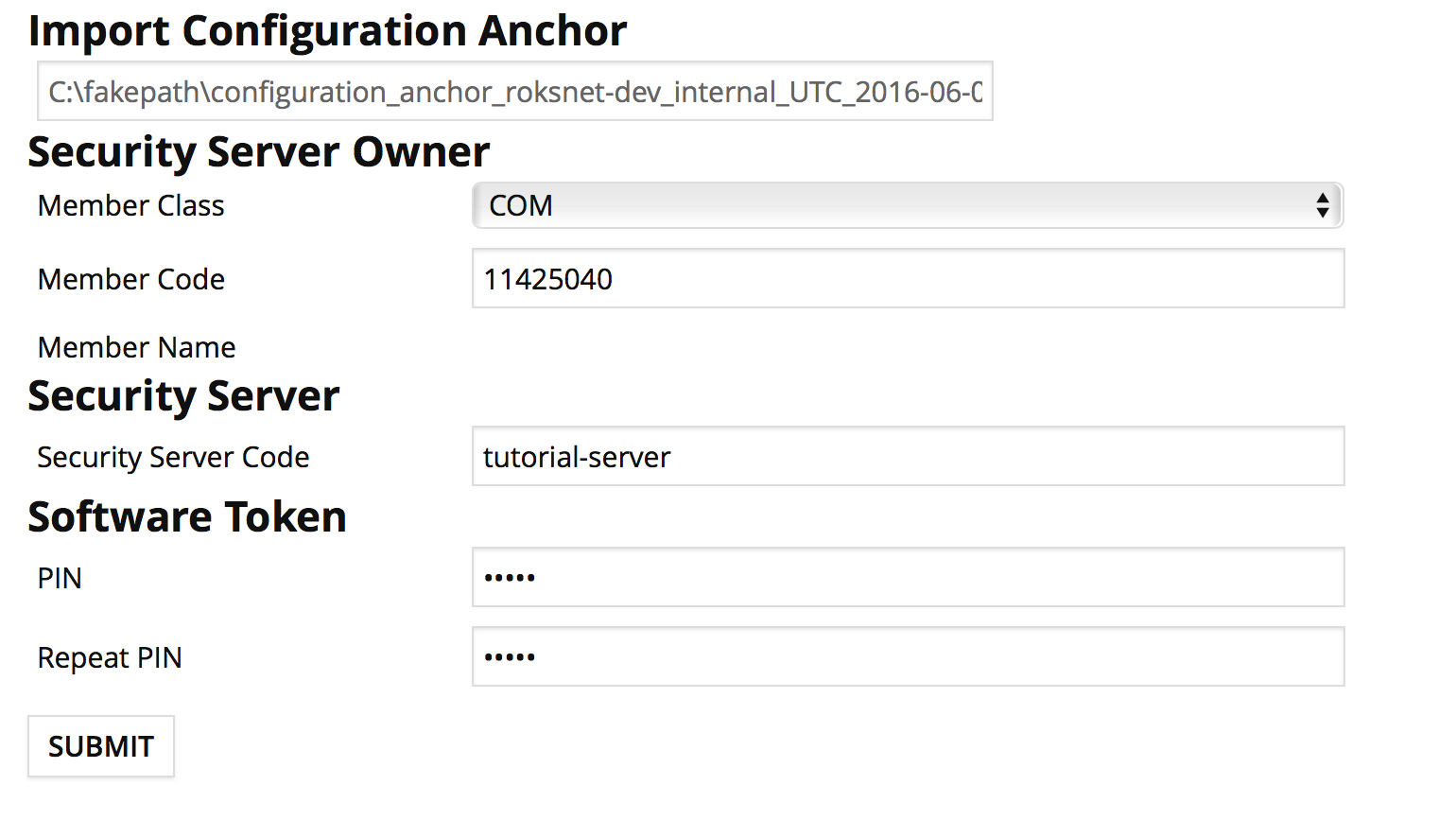
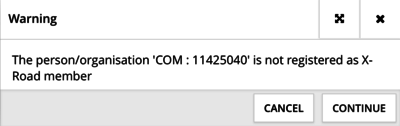
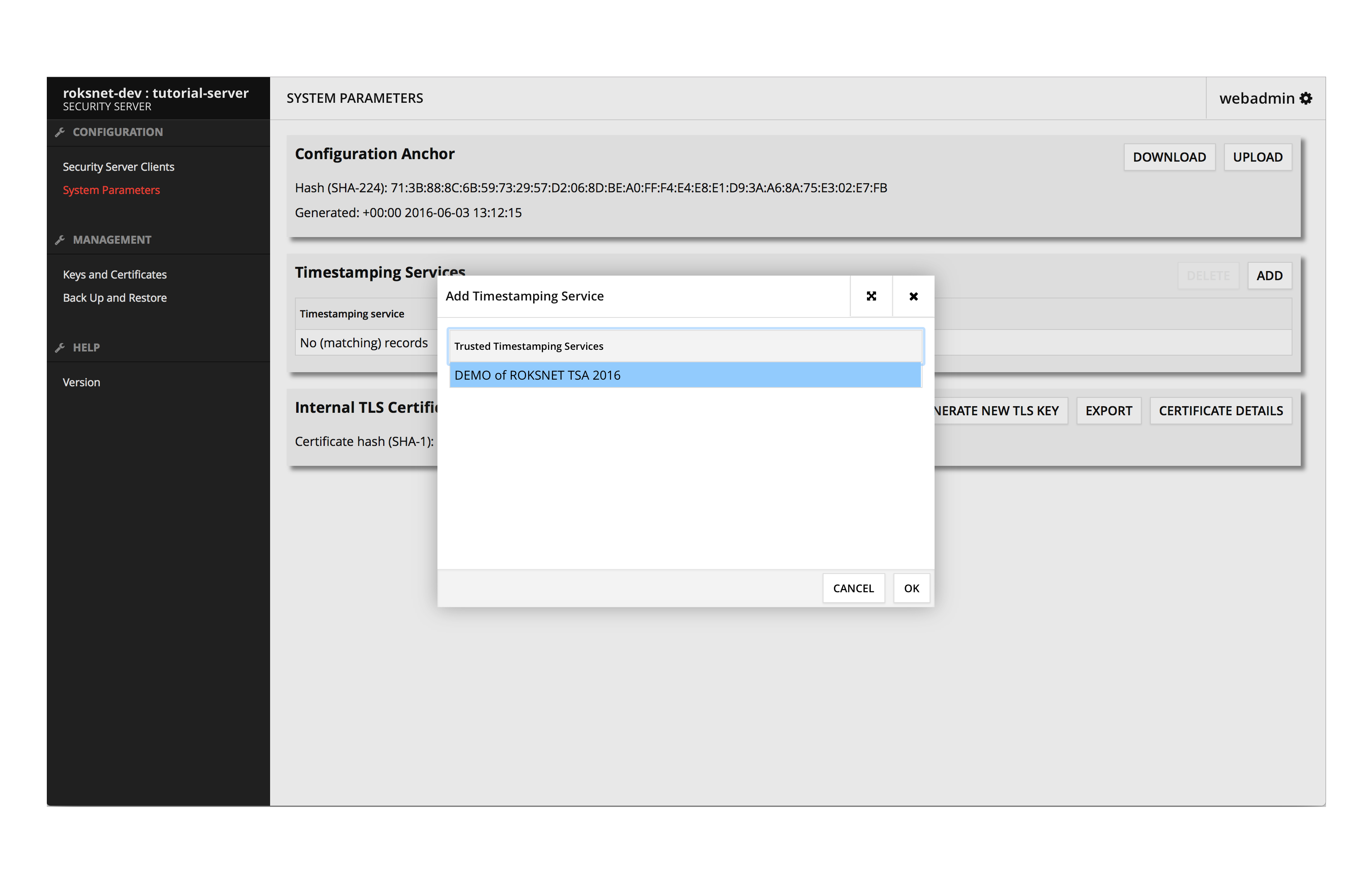
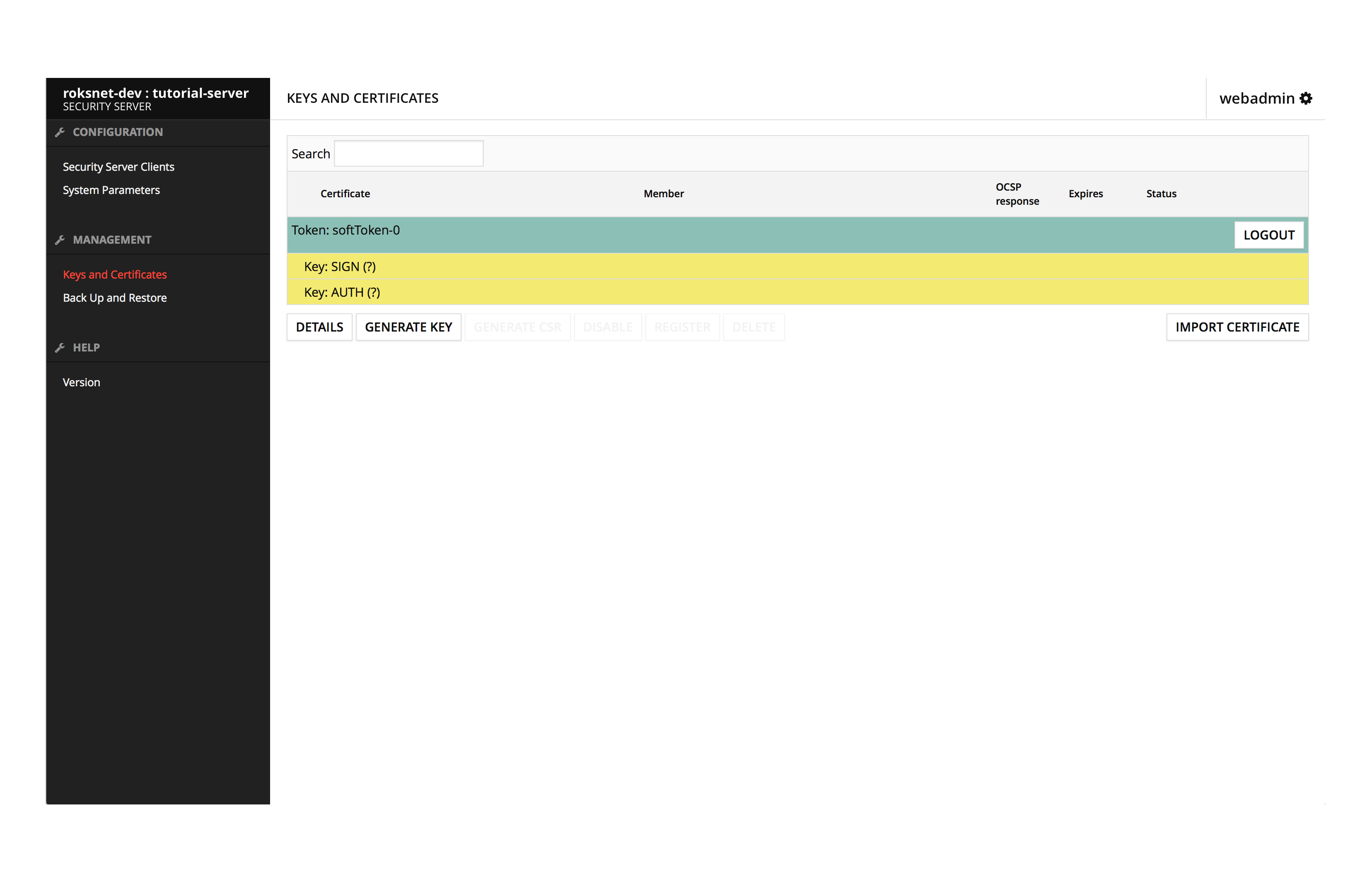
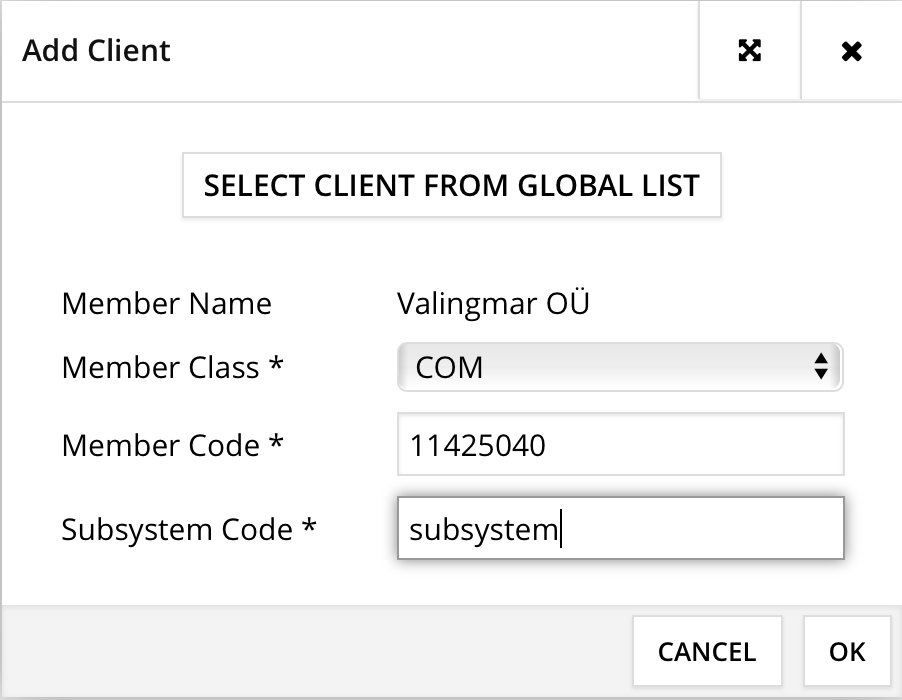
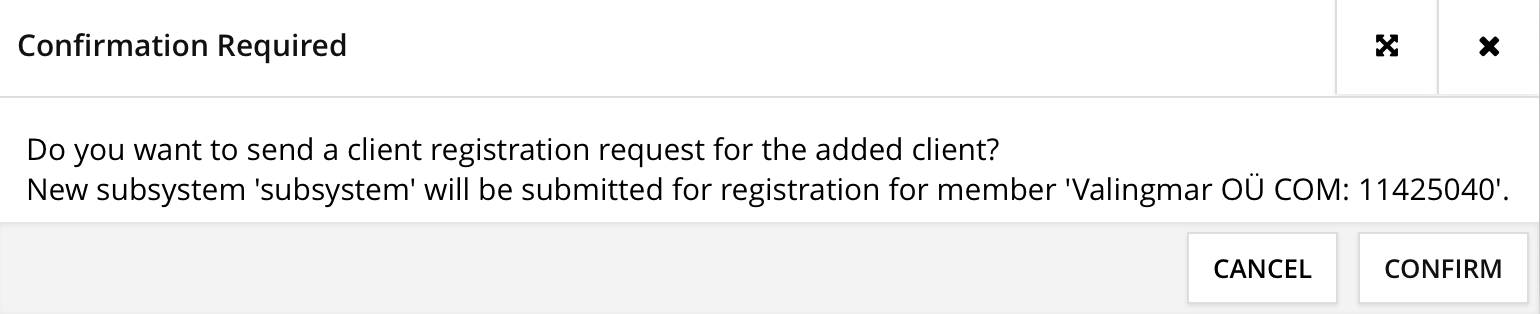
5. Setup security server
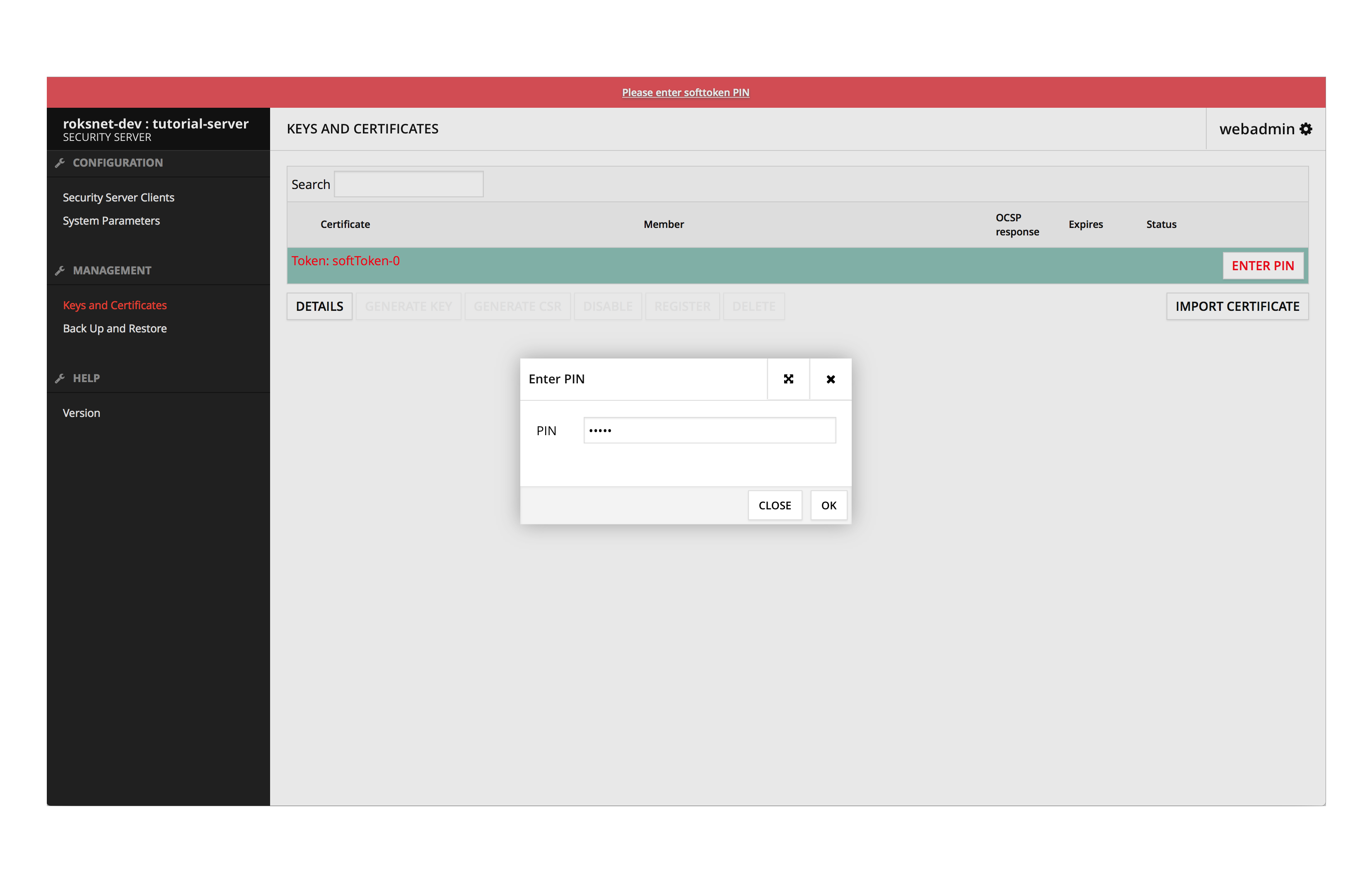
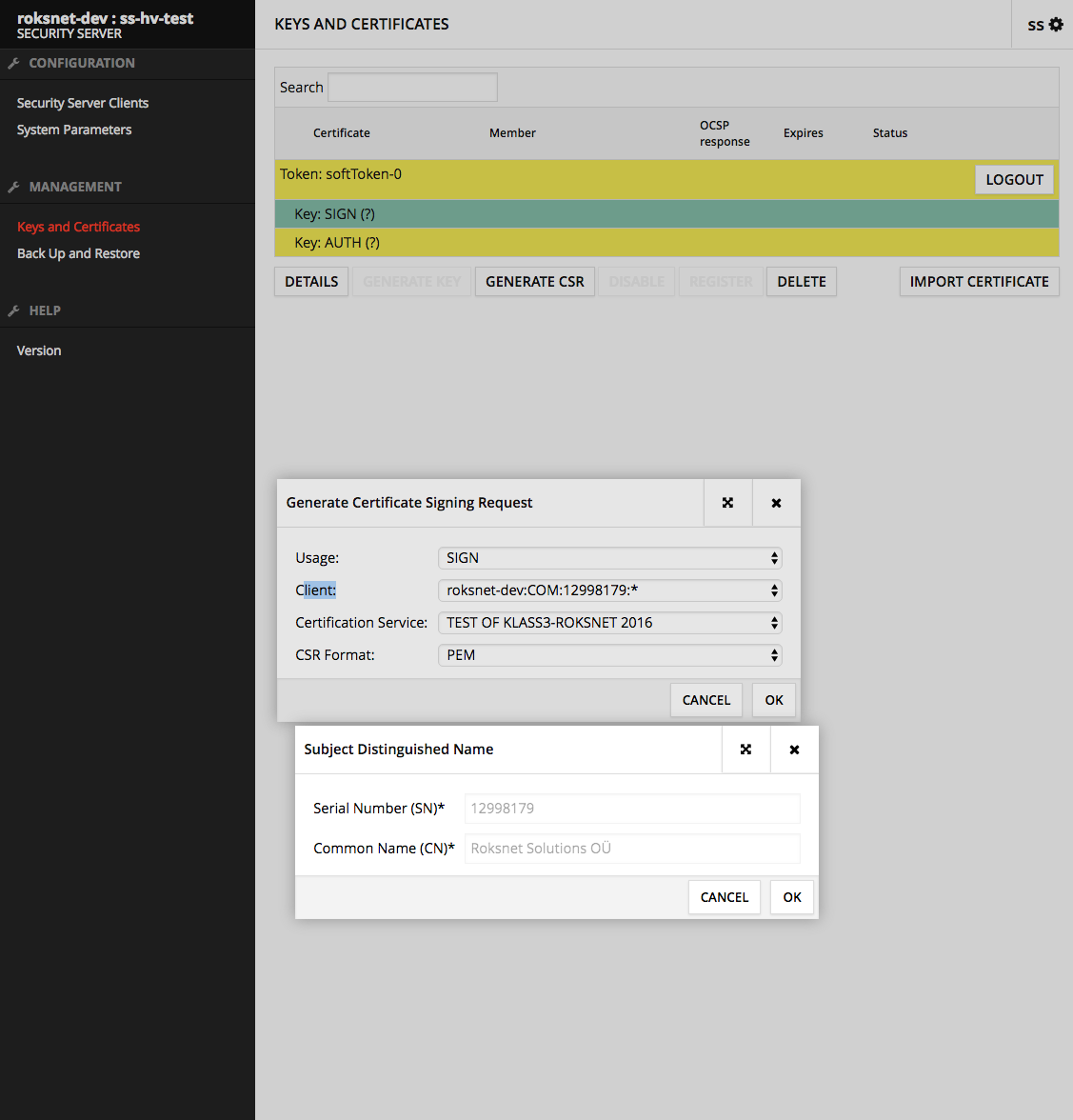
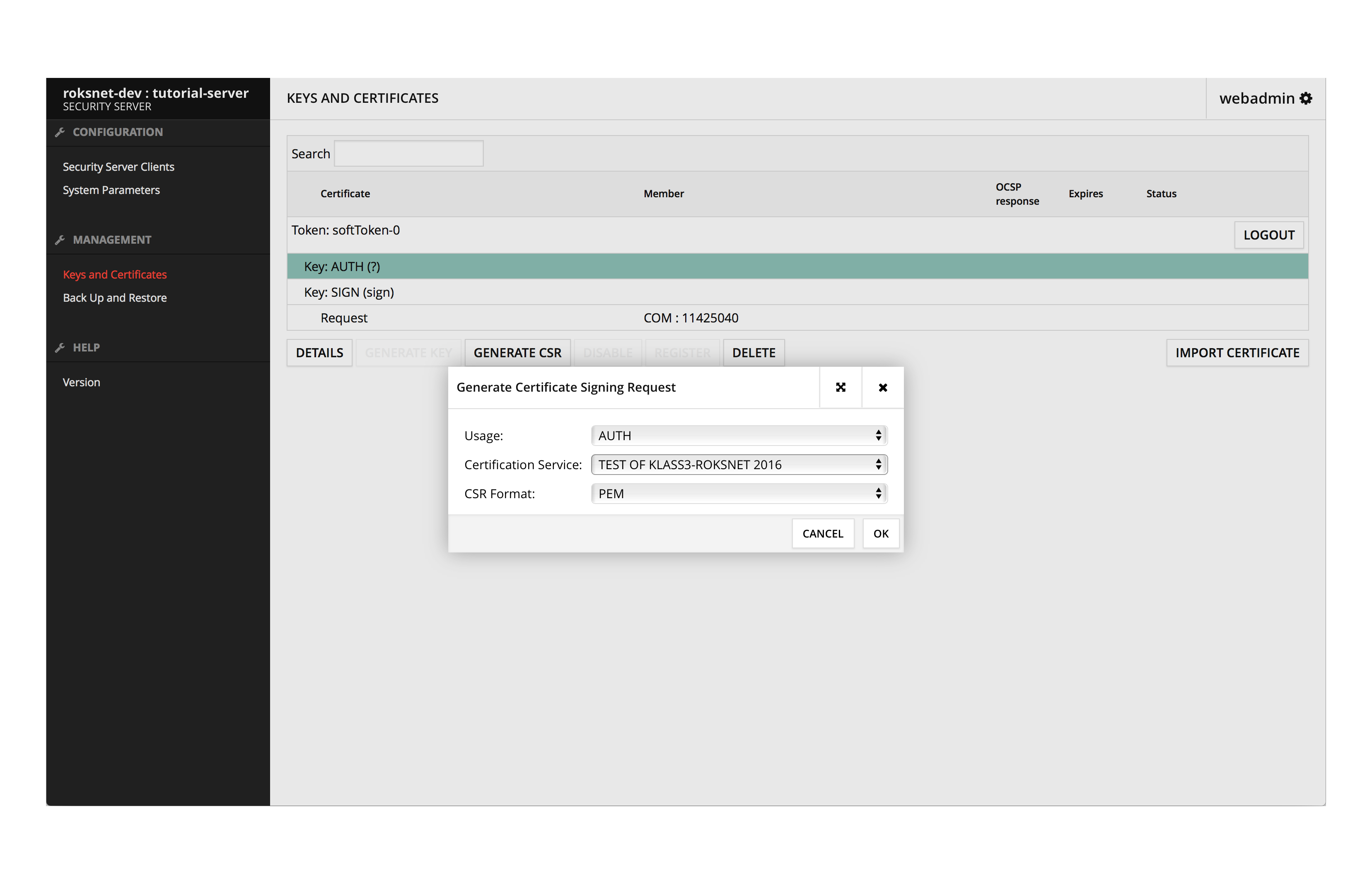
6. Send CSRs
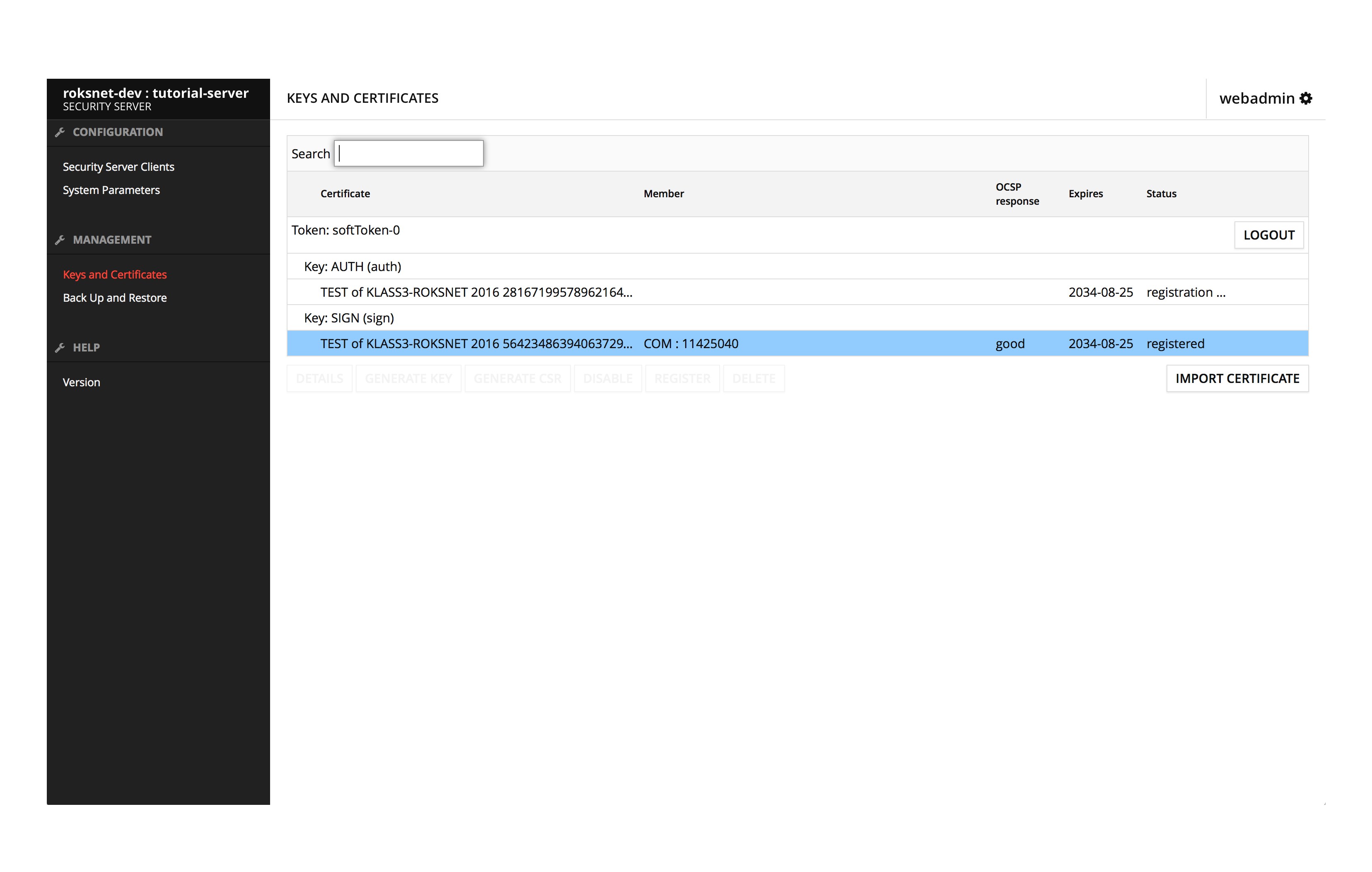
7. Import Certificates
In order to start using Roksnet, You will need to set up a Security Server. Security Server provides a secure way to communicate with other members in the network.
Security Servers main roles are to provide authentication and verification of messages, that are transmitted peer to peer between members. Security server also provides access control toward your own information system, if you are a service provider.